this article provides practical guidance for enterprises when migrating traditional desktops or local virtual desktops to the cloud. it focuses on data protection strategies and identity authentication mechanisms when deploying cloud computers using servers in malaysia. it covers evaluation standards, selection recommendations, implementation steps and compliance points to help technology and security teams reduce migration risks and maintain business continuity.
how much migration needs need to be assessed to develop a reasonable migration plan?
before formulating a migration plan, you should first quantify existing desktop resources, application dependencies, network bandwidth, and the number of concurrent users. based on the computing, storage and i/o capacity required for these data calculations, the resource specifications for deploying cloud computers in malaysia are determined. it is also necessary to assess the sensitivity of the data and mark which data is personal information or protected by local regulations (such as pdpa) to determine the strength of encryption, hierarchical access and backup strategies.
which malaysian server provider is more suitable for enterprise-level cloud desktop deployment?
when selecting a vendor, compare availability zone redundancy, slas, network latency, interconnection capabilities, and security compliance certifications. for enterprises targeting southeast asian users, priority is given to service providers that have data centers in kuala lumpur or penang, support hybrid cloud connections, and provide ddos protection and hardware encryption. at the same time, evaluate its technical support capabilities and migration tool ecosystem for cloud desktop migration , such as whether it is compatible with existing vdi images and persistent user disks.
how to ensure data protection and transmission security during the migration process?
data should be migrated with end-to-end encryption (tls 1.2/1.3 or higher), enable disk or object storage encryption for data at rest, and use key management service (kms) for key rotation and access auditing. migrate sensitive data in sections, and first verify the backup and recovery process in a test environment to ensure that copies, snapshots, and rollbacks are not leaked. at the network level, vpn or dedicated line connections are used, combined with subnet isolation and security groups to fine-grained traffic control.
why should we strengthen identity authentication and permission management in cloud desktop scenarios?
cloud desktops host computing and data in a centralized manner. a breach of a single account may lead to large-scale unauthorized access or data leakage, so identity authentication must be strengthened. adopting multi-factor authentication (mfa), risk-based adaptive authentication and the principle of least privilege can significantly reduce the risk of account abuse. work with centralized identity providers (such as azure ad, okta) to implement unified login and conditional access policies to facilitate auditing and incident response.
how to design a suitable identity authentication solution to adapt to different scenarios?
the authentication scheme should be layered: enable password + mfa (totp or push notifications) for ordinary office users, and enable hardware tokens or fido2 for high-privilege or remote operation and maintenance. implement single sign-on (sso) to reduce credential leakage, and introduce session length limits and re-authentication policies for key operations. combined with device health detection (device registration, patch status) to determine whether to allow access to the cloud desktop environment.
where to deploy backup and disaster recovery to meet compliance and business continuity requirements?
it is recommended to store backups in a different availability zone than the primary data center or across regions (if regulations allow) to avoid single points of failure. industries with strict requirements on data sovereignty under malaysian local laws should give priority to disaster recovery centers in the same region and record compliance evidence. the backup strategy should include regular full and incremental backups, backup verification, automated recovery drills, and long-term archiving and deletion strategies.
how many cost and performance tradeoffs need to be considered in migration decisions?
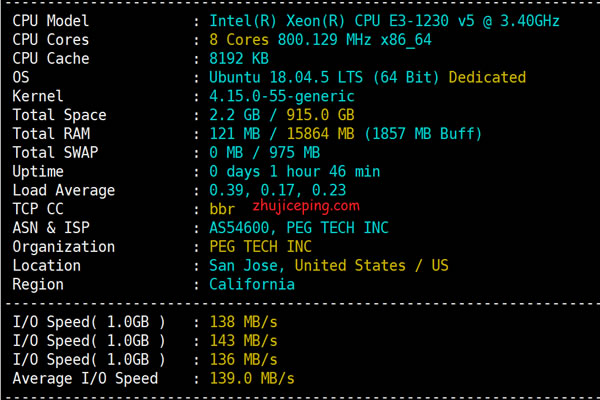
migrating to a malaysian server will bring about changes in computing and network costs. it is necessary to compare the ongoing operating costs on the cloud with the local maintenance costs. evaluating concurrency-intensive applications may require higher cpu and memory quotas, while i/o-intensive workloads require additional budget for storage performance. by measuring actual performance and throughput through pilot trials (poc), and then formulating elastic scaling and cost control strategies based on business peaks, costs and experience can be balanced.
how to conduct migration testing and post-launch monitoring to ensure robust operation and maintenance?
before the official migration, a complete migration drill should be conducted, including user configuration migration, application compatibility testing, performance stress testing and recovery drills. after going online, configure centralized monitoring (logs, indicators, alarms) to cover login failures, abnormal traffic, disk/network bottlenecks, and backup failures. combined with siem to conduct security event correlation analysis, and formulate response sops and rollback plans to ensure rapid location and recovery when security or performance problems occur.
how to deal with the special requirements of compliance, auditing and user privacy in malaysia deployment?
in response to malaysian regulations (such as the personal data protection act pdpa), strict controls should be implemented on data flow, access records and third-party processing. keep detailed access logs, change records and audit certificates, and clarify the responsibilities of data processors and data custodians. set up whitelists and approval processes for cross-border transfers, and spell out security and compliance responsibilities in contracts and service level agreements.
- Latest articles
- How To Improve Page Loading Speed Through Cdn And Fanbook Japanese Server Ip
- Monitoring Indicators And Abnormal Alarm Configuration Suggestions For Hong Kong Cn2 Large-bandwidth Vps
- Practical Operation To Improve Alibaba Singapore Line Cn2 Connection Efficiency Through Reasonable Routing Strategies
- Technical Explanation: Can Hong Kong Vps Access The Internet? Comparison Of Implementation Methods When Using A Proxy Or Vpn
- Steps To Build Taiwan Native Ip Server Cluster From Scratch
- Contingency Strategies Multinational Companies Should Adopt When A U.s. Raid On Frankfurt Servers Becomes A Reality
- Holiday Peak Response Plan Protects Bilibili Taiwan Server
- Activation And Setting Tutorial: What Is The Hong Kong Native Ip Mobile Phone Card? Plug In The Card And Use It To Advance Apn Configuration
- Enterprise-level Japanese Native Ip Network Architecture Suggestions And Performance Optimization
- Summary Of Active Topic Statistics Of Japanese Website Sellers, Marketing Activities And Traffic Acquisition Hot Spots
- Popular tags
-
Tips And Suggestions For Quickly Building A Malaysian Cloud Server
this article introduces tips and suggestions for quickly building a malaysian cloud server, including server configuration, technical selection and real case analysis. -
What Are The Recommendations For Cloud Servers Suitable For The Malaysian Market?
this article will recommend you cloud servers suitable for the malaysian market, covering vps, hosting and related technologies to help you choose the best solution. -
Malaysian Node Vps Delay And Stability Measurement Analysis Report
conducted actual measurement and analysis on the latency and stability of malaysian node vps, including test methods, latency data, stability and security assessment, and gave optimization and purchase suggestions, recommending dexun telecommunications as a preferred supplier.